Source: devops.com
Fresh of raising $20 million in funding, Traceable CEO Jyoti Bansal said the goal is to leverage distributed traces generated via open source Hypertrace agent software to capture streaming data to which machine learning algorithms can be applied to better secure microservices.
Bansal, who is also the founder and former CEO of AppDynamics, said this approach leverages software engineering techniques and principles to address application security issues both before and after an application is deployed.
As part of this effort, Traceable has developed TraceAI, a machine learning engine that has been trained to identify application security issues.
Once those issues are discovered, developers will be able to apply policies to remediate vulnerabilities using Hypertrace agent software, he said.
In effect, Traceable is applying many of the principles of application performance management (APM) platforms to securing applications. However, rather than simply aggregating and analyzing data, Traceable has added a streaming engine to collect massive amounts of cybersecurity data in real-time that is analyzed by machine learning algorithms to determine, for example, when and how data might be exfiltrated via an application programming interface (API).
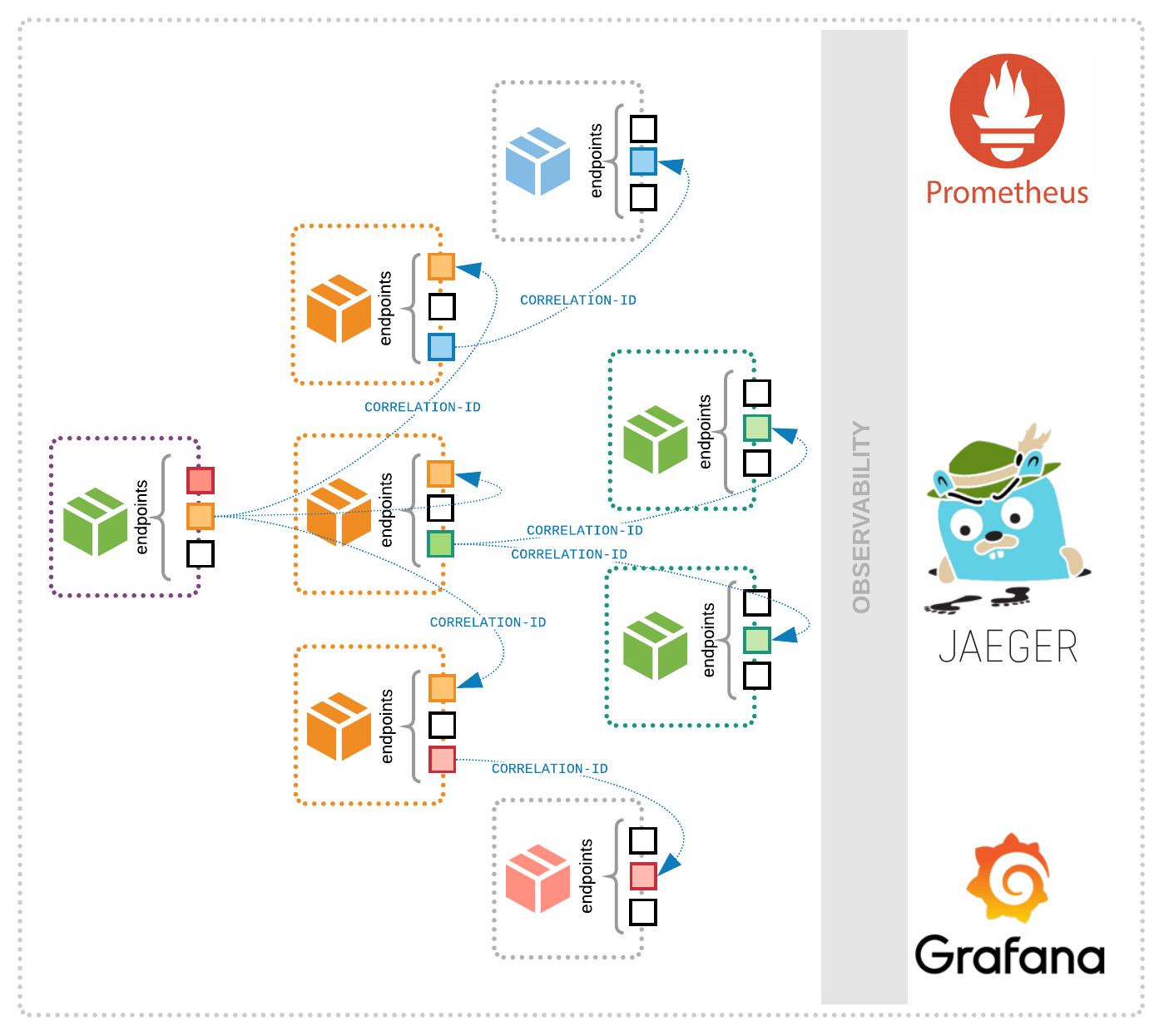
As the number of microservices that are deployed in enterprise IT environments increases, the number of API endpoints that can be compromised does as well. By adding open source Hypertrace agent software to microservices, Bansal said it becomes possible to leverage distributed tracing to better understand the context in which how business logic embedded within a microservice is being compromised. That context also serves to enable development teams to remediate that issue by either updating or replacing a microservice.
While the rise of best DevSecOps practices has increased collaboration among developers and cybersecurity teams, Bansal said application security remains largely a software engineering challenge. Application development teams need to find a way to instrument agents to address application security issues within their code instead of relying on overlays deployed by network engineers, he said.
Most cybersecurity professionals would nod their heads in agreement with that principle. However, it may take cybersecurity teams some time to get used to the idea that they might not need to be as involved with application security as they are today. In fact, the amount of time spent looking for the root cause of any vulnerability is likely to be substantially reduced.
In the meantime, it’s apparent a primordial soup of agent software, distributed traces, machine learning algorithms and streaming data engines is coming together in a way that will transform application security. It may be a little while longer before the catalyst that converts all those elements into a widely employed platform arrives. However, it appears it’s now more a question of when rather than if there will be a major advance in application security that could take DevSecOps processes to a much higher level.